Theme 1: AI-Driven Piracy — The 2026 "Agentic" Shift in App Cracking.
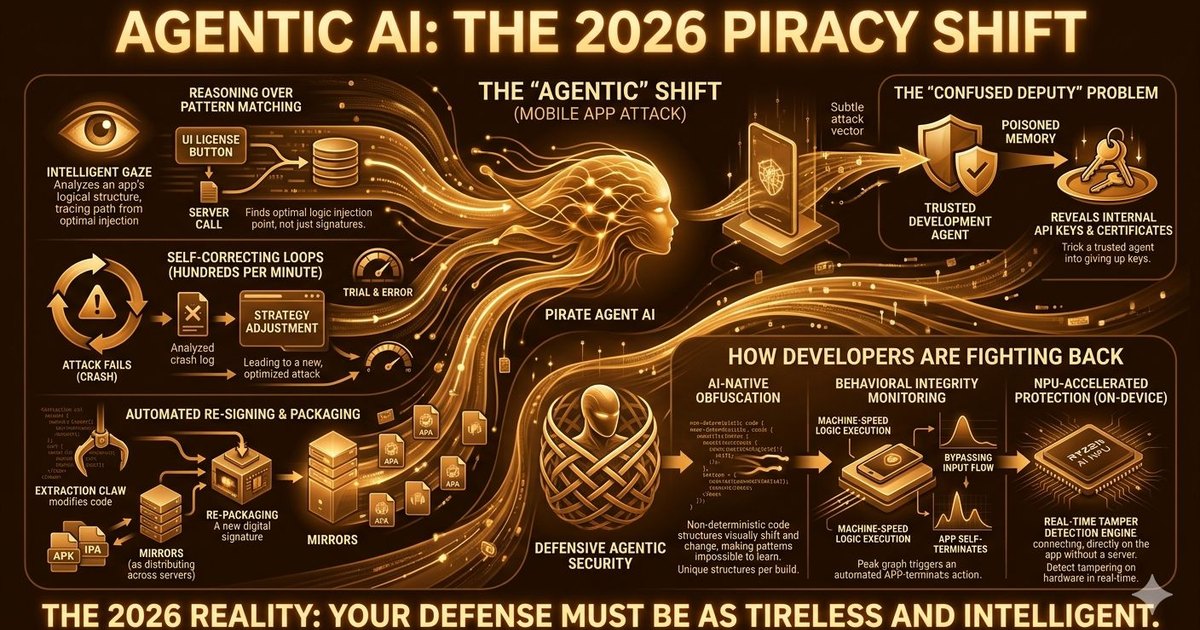
As we move through 2026, the "script kiddies" and manual crackers of the past have been replaced by a much more formidable opponent: Agentic AI. This shift marks a permanent change in how mobile applications are attacked, moving away from human-led debugging to autonomous, machine-speed exploitation.
What is the "Agentic" Shift?
Unlike standard generative AI, which might help a human write a snippet of code, Agentic AI systems are autonomous actors. In the world of piracy, these "Pirate Agents" are programmed with a single goal: Find a way to bypass the license check and re-package the app.
- Reasoning over Pattern Matching: Traditional scanners look for known signatures. Agentic AI actually "understands" the logic of your code. It can trace a license check from the UI button all the way to the server call and decide the best point of injection.
- Self-Correcting Loops: If an AI agent tries to crack your app and fails because of an integrity check, it doesn't stop. It analyzes the crash log, adjusts its strategy, and tries again—completing hundreds of "trial and error" cycles in minutes.
- Automated Re-signing: Once the logic is bypassed, the agent automatically handles the extraction, modification, and re-signing of the APK/IPA, distributing it to multiple mirrors before you even receive a first alert.
The "Confused Deputy" Problem
One of the most dangerous trends in 2026 is the Confused Deputy attack. Pirates are now targeting the AI agents you use for development or customer support. By "poisoning" the memory of a trusted agent, they can trick it into revealing your app's internal API keys or security certificates, effectively giving the pirates the keys to your front door without them ever having to break a lock.
How Developers are Fighting Back
Static defenses are no longer enough. To survive in 2026, your app security must be as "agentic" as the attackers:
- AI-Native Obfuscation: Using local AI tools to create non-deterministic code structures that change with every build, making it impossible for a pirate agent to learn a single pattern.
- Behavioral Integrity: Instead of checking for a modified file, apps now monitor "behavioral anomalies." If an app is executing logic at machine-speed or bypassing standard user input flows, it self-terminates.
- NPU-Accelerated Protection: Leveraging local hardware (like the Ryzen AI NPUs) to run security models directly on the device, detecting tampering in real-time without needing a server connection.
The 2026 Reality: We are no longer in an era of "Set and Forget" security. When the enemy is an autonomous agent that never sleeps, your defense must be equally tireless and intelligent.
